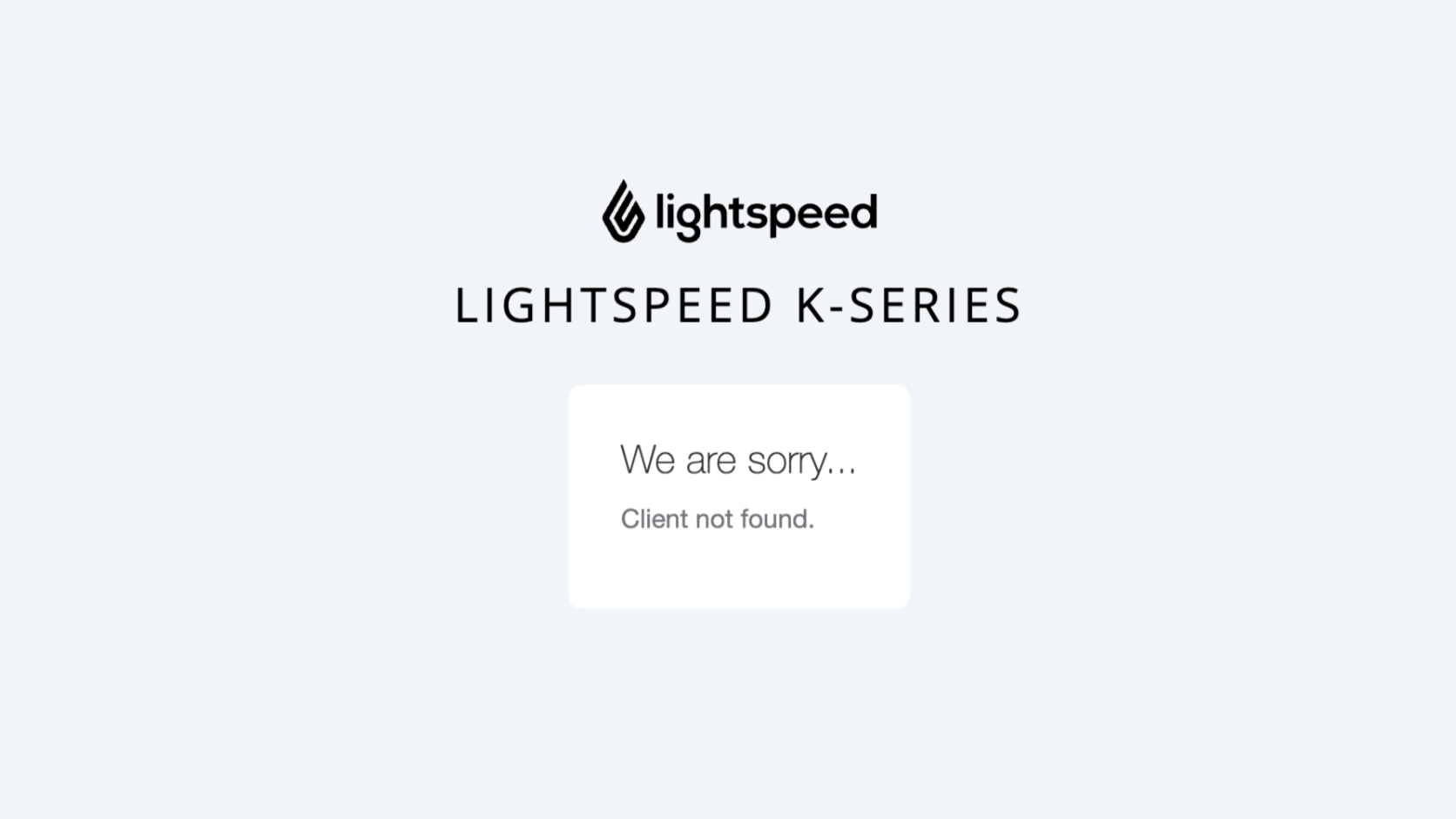
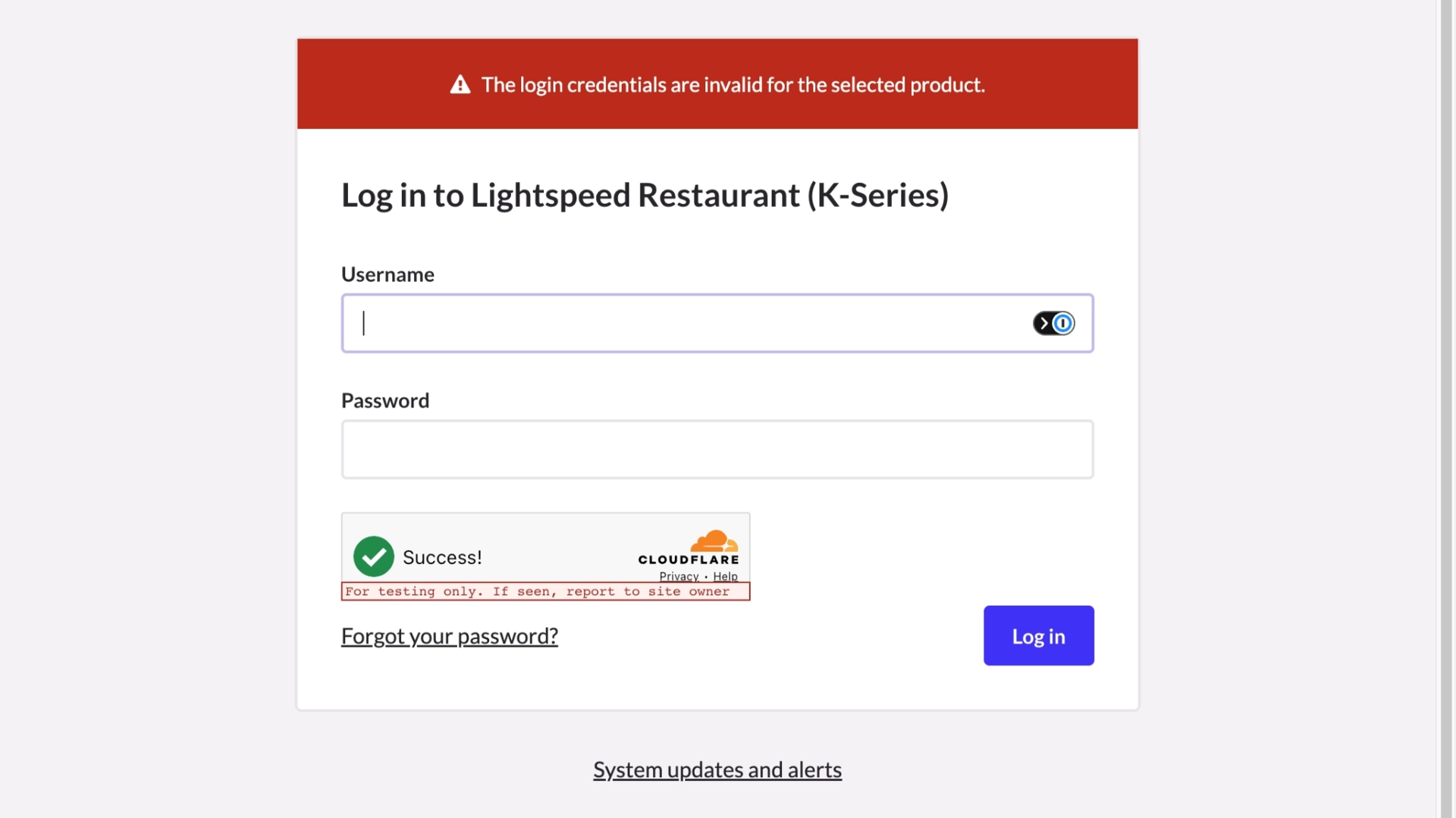
Error: Client not found
-
Client ID:
devp-v2-demo-dasxtrial-b69ffe954c5cd33c57a79a94780eb2ab— belongs to trial (prefix:devp-v2-demo) - Authorization URL used:
https://auth.lsk-prod.app/realms/k-series/protocol/openid-connect/auth
?response_type=code
&client_id=devp-v2-demo-dasxtrial-b69ffe954c5cd33c57a79a94780eb2ab
&scope=financial-api
&redirect_uri=https%3A%2F%2Flocalhost%2F📝 Note
The URL targets
lsk-prod.app (production), but the
client_id is a trial client.
These environments are isolated — clients are not shared.